Major Findings
· The Cyber Risk Principles developed by the ISA, NACD and the World Economic Forum help drive cyber resilience across industries.
· Simulation-aided research from MIT CAMS shows that commitment to and adoption of the Cyber Risk Principles significantly improves cyber resilience.
· Results also show that, commitment to these cyber risk principles does not raise costs.
In 2021, the World Economic Forum and its partners, with the National Association of Corporate Directors (NACD), Internet Security Alliance (ISA) and PwC, published the Principles for Board Governance of Cyber Risk (Consensus Cyber Risk Principles), critical to driving resilience across industries. This guidance (initially developed for corporate boards of directors) is summarized in six principles:
· Recognize that cybersecurity is a strategic business enabler.
· Understand the economic drivers and impact of cyber risk.
· Align cyber risk management with business needs.
· Ensure organizational design supports cybersecurity.
· Incorporate cybersecurity expertise into board governance.
· Encourage systemic resilience and collaboration.
These principles represent a significantly different approach to resilience compared to how organizations traditionally delegate cyber security to IT. This typical approach created a misplaced perception of the strategic nature of cyber risk.
This misplaced perception of the strategic nature of cyber risks can have enormous consequences. However recently released MIT research shows that “adopting Cyber Risk Principles promoted by WEF, ISA and the NACD demonstrates that individual organizations can significantly improve their cyber resilience without raising costs.”
— Sander Zeijlemaker, Research Affiliate Cybersecurity at MIT Sloan (CAMS), Managing Director Disem Institute | Michael Siegel, Principal Research Scientist, Director, Cybersecurity at MIT Sloan (CAMS) | Daniel Dobrygowski, Head of Governance and Trust, World Economic Forum
Understanding through simulation
With cyber risk a vital issue on leaders’ agendas, MIT CAMS has developed a method to improve leaders’ abilities to foresee and manage cyber risks. This technology, referred to as a cyber risk dashboard, is grounded in control theory and system dynamics and is built on significant research in the field, including interviews with chief information security officers (CISOs). It has been validated over the years at a Fortune 500 company by analyzing a wide range of strategic cyber risk challenges.
The dashboard closely mimics the cyber risk decision-making ecosystem. It considers current defence posture and development of attack tactics, emerging cyber incidents and changing organizations in terms of people, processes and technology. The cyber risk dashboard provides the means to make projections according to the performance indicators of an organization’s cybersecurity strategy. This work can be easily adapted for other strategic analyses. MIT CAMs used a simulation added approach to understand organizational behavior when adapting the consensus Cyber Risk Principles.
The use of personas – artificial decision-makers profiles with specific characteristics that drive their cyber risk management strategy – is a scientifically grounded approach to exploring the behavioural side of cyber risk management. Using the personas of different organizations to drive strategic decision-making, this simulation technology can foresee the future impact of their strategy. In this analysis, we also reuse data from our anonymized case study at a Fortune-500 company called Smart Wealth Management Inc. As such, we recognize:
The cyber-conscious CEO (CC-CEO)
This CEO might be aware of the principles but has yet to adopt them. This CEO focuses on reasonable compliance with security standards and controls security costs. Increasing workload and lack of security resources drives a more reactive approach to cyber risk.
The resilient CEO
This CEO is cyber-conscious but has gone further by adopting the consensus Cyber Risk Principles to foster resilience. This CEO has a proactive and anticipatory approach to threats, knows how their technology drives their business and focuses on maintaining business performance and cyber risk cost predictions.
Strategic awareness fosters cyber resilience
We observe a significant difference when comparing the strength of defence posture represented by the number of security incidents/compromised assets. The CEO who follows the consensus Cyber Risk Principles is predicted to have up to 85% fewer cyber incidents (see Figure 1) compared to the traditional CEO.
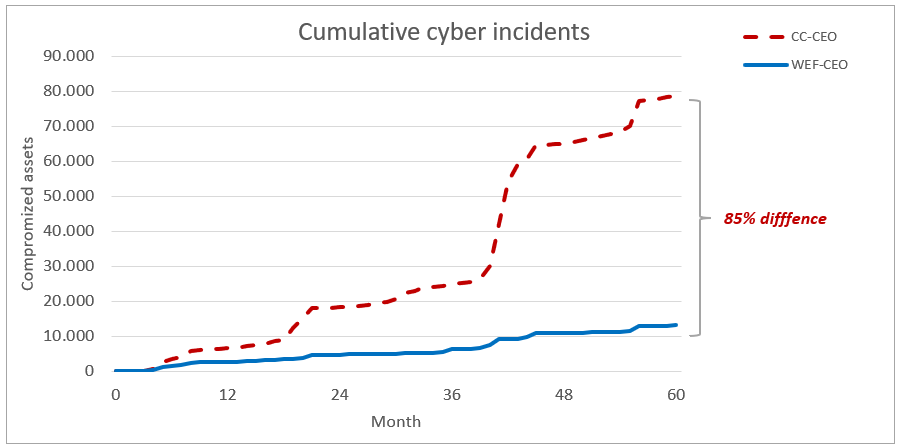
Figure 1. Cumulative incidents over 60 months for cyber risk management strategy of the CC-CEO and the consensus principle CEO. Image: MIT CAMS
The cyber risk efforts and task prioritization of the CEO who follows the consensus principle allows for early early intervention that limits adversarial behaviour, whereas the traditional CEO’s team often responds slower, which ultimately benefits the adversary.
Similar insights can be observed in the risk profile (see Figure 2) regarding a frequency distribution of potential cyber incident occurrence in favour of the consensus principle CEO, mainly when vast numbers of cyber incidents may require the IT teams to help the security teams. These situations, known as spill-over effects, require IT task reprioritization, usually at the expense of IT project delivery.
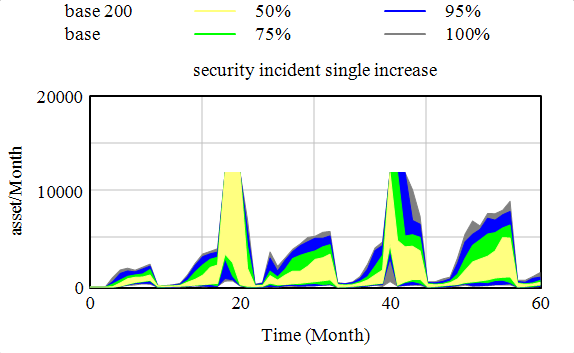
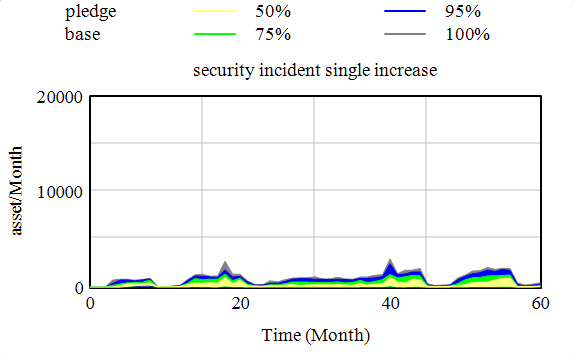
Figure 2. Cyber risk profile is based on the distribution of potential security incidents occurrence over 60 months for cyber risk management strategy of the traditional CEO and the CEO following consensus principles. Sensitivity analysis is performed with a 95% certainty range. Adopting the consensus Cyber Risk Principles demonstrates that individual organizations can significantly improve their cyber resilience without raising costs. Image: MIT CAMS
A resilient approach does not raise costs
The CEO following the consensus principles likely has lower costs compartment with the traditional CEO (see Figure 3). The major difference between these two scenarios is in the allocation of task priorities and cyber risk efforts of the security staff. The traditional CEO has ongoing efforts that require additional staff resources to support response and recovery processes, execute post-mortem research and adjust and improve security capabilities accordingly. In contrast The CEO following the consensus principles implemented security by design has an ongoing proactive capability adjustment and improvement (including continuous automation) and has implemented regular board-level cyber risk dashboarding and reporting.
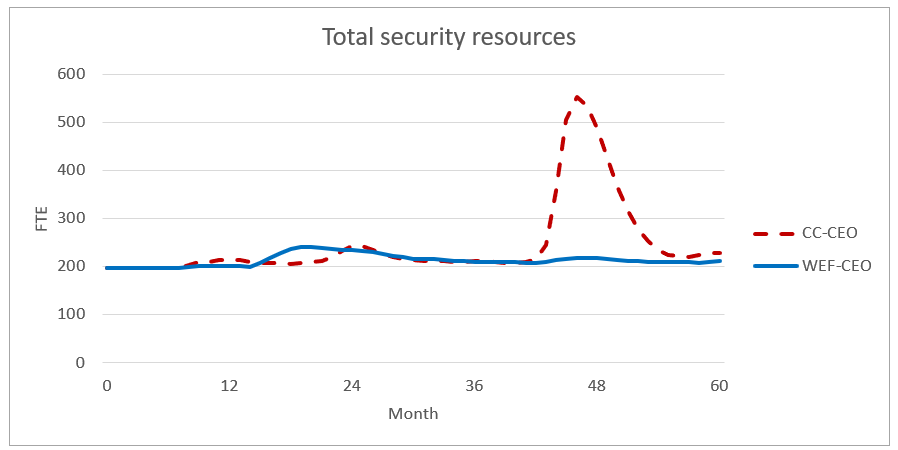
Figure 3. Resourcing (FTE) 60 months for cyber risk management strategy of the CC- CEO and the WEF-CEO. Image: MIT CAMS
Adopting the consensus Cyber Risk Principles demonstrates that individual organizations can significantly improve their cyber resilience without raising costs. In these simulations, adopting the principles proved valuable. In practice, interconnectedness and connectivity between organizations introduces new interdependencies, which will be explored through further research and simulations. The current findings in themselves, however, make a strong case for organizations to adopt the Forum’s Cyber Risk Principles.
MIT’s work is co-funded by Fondo Europeo di Sviluppo Regionale Puglia POR Puglia 2014 – 2020 – Asse I – Obiettivo specifico 1a – Azione 1.1 (RS) – Titolo Progetto: Suite prodotti Cybersecurity e SOC and BV TECH S.p.A. and co-funded by Cybersecurity at MIT Sloan (CAMS).
