WHAT IS BEST FOR SEC ON CYBER? OLD STYLE REGS OR NACD MODEL?
To begin with, we know the cyber risk oversight model described in the NACD-ISA Cyber Risk Handbook actually enhances cybersecurity. We also know there is no proof the SEC proposed regulations, which have already been tried in multiple venues, will enhance cybersecurity or protect investors. In fact, the NACD-ISA handbook is the only set of […]
Larry Clinton interviewed on CNN Question International – Marriott Cyber Breach – November 30, 2018
DIGIT INTERVIEWS – Larry Clinton, Cyber Security Expert

In an increasingly digital world, where the Internet is starting to define and control our very existence, threats to the system are wide-ranging and with debilitating effects.
Google: NSA Isn’t Snooping
On his June 12th Fox Business News appearance, ISA President Larry Clinton rebutted the notion that the private sector is providing the National Security Agency “unfettered access” to all of its data. Clinton stressed the fact that companies safeguard their data because it is in their business interests to do so. He also noted the […]
Defending Cyber Attacks

On February 13, 2013, following the release of the Obama administration’s Executive Order 13636, CNBC’s “Power Lunch” asked ISA President Larry Clinton to appear on the show to discuss how the order will impact the private sector and solicit ISA’s view on its implications.
CNBC: Cyber Attack Warning

Corporate America’s Cyber Defense

BILL WOULD HAVE BUSINESSES FOOT COST OF CYBERWAR
By Tom Gjelten Business executives and national security leaders are of one mind over the need to improve the security of the computers that control the U.S. power grid, the financial system, water treatment facilities and other elements of critical U.S. infrastructure. But they divide over the question of who bears responsibility for that effort. […]
Security Legislation: IT Insider with ISA’s Larry Clinton

There are a number of cybersecurity bills hotly debated on Capitol Hill and more than one government agency vying to “own” cybersecurity for the nation. So with all of this disagreement, how can lawmakers, security agencies and businesses find a way to work together to protect our safety and our intellectual property?
Cyber Security and the Private Sector
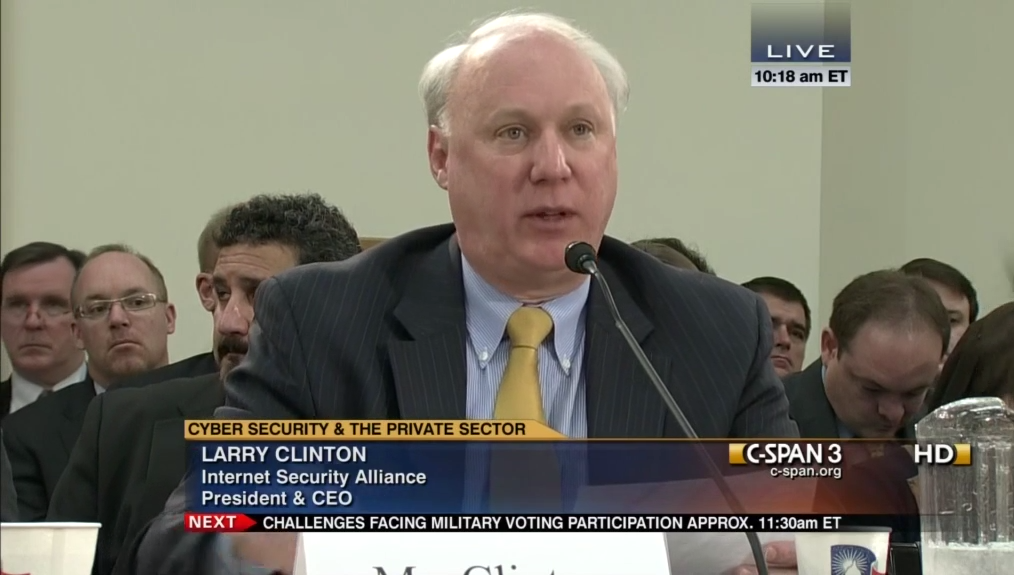
House Energy and Commerce Subcommitte on Communications and Technology Witnesses testified on cybersecurity threats to the U.S., and the role of the private sector and federal government in addressing those threats. They focused on cyber threats to small businesses, communications companies, mobile technology, cloud computing, and smart phone applications. Other topics included federal legislation on […]

